Whether by e-mail, text message or telephone, people are increasingly being asked to carry out actions aimed at disclosing personal or confidential information in order to extort money from them. Expired products, blocked accounts, stolen old passwords, allegedly hacked computers, intimate videos threatened to be shared with your contacts – AI is increasing the creativity of cybercriminals who trick their victims with increasingly credible messages that perfectly imitate the identities of well-known brands.
What is phishing or phishing?
Criminal uses phishing to try to get their victims to divulge their passwords and other personal information with the aim of obtaining money or accessing their accounts. The word phishing is derived from the contraction of the words password and fishing and literally means “password fishing”. In French, we speak of “hameçonnage”.
More specifically, these are messages that are made to look like communications from trusted companies with the aim of stealing credentials from the most gullible people, either by returning an email or via a web form hosted on a hacked or fraudulent site that imitates the identity of a trusted company.
In order to gain your trust, these malicious messages may contain personal information such as your first name, your domain name and its expiry date or passwords that you always use. The authors of these malicious emails get their hands on this information from public directories such as the Whois or exploit security vulnerabilities of known websites where you might have legitimately entered this information.
These fraudulent campaigns can also play on the urgency of renewing an expired product or the risk of permanent data loss, or can scam victims through emotions or threats.
It is therefore essential to use a secure messaging service and to know how to defeat this threat.
How to detect and protect yourself from phishing?
1. Use a secure messaging service
Infomaniak’s email services include automatic protections against viruses, potentially dangerous messages and fraudulent links. They also alert you when you reply to a message from an unknown sender and allow you to report suspicious messages.
2. Check the authenticity of your messages
Emails from Infomaniak and large companies are generally authenticated by this blue badge, which appears in Infomaniak Mail as follows:
This badge certifies that the message comes from Infomaniak or a legitimate company, and not from someone trying to impersonate their identity. If you are unsure about an Infomaniak invoice, log in to your Infomaniak Manager to check your invoices and the status of your services.
3. Check the links you click on
Never click on links or open attachments if in doubt. If the message concerns Infomaniak, make sure that the address of the landing page in your browser contains the domain infomaniak.com before clicking on a link.
Examples:
- infomaniak.com (spelling must be perfectly accurate):
- manager.infomaniak.com/XYZ
- faq.infomaniak.com/XYZ
- infomaniak.com/XYZ
- news.infomaniak.com/XYZ
- and so on.
4. Never share sensitive information
Never disclose your bank or credit card details and never send copies of your passport or ID card to strangers. They could use this information to impersonate you to third parties.
5. Do not give access to your computer
Never give strangers access to your computer, even via the Internet. Fraudsters could steal your data, initiate transactions, block your computer and extort money from you. Infomaniak will never ask you for personal or banking information by email.
6. Never transfer money
Never be persuaded – even over the phone – to share data, hand over money or transfer money. Verify the authenticity of a call by calling back the authority or company number as it appears on their official website. If you’re in doubt, here’s Infomaniak’s official contact page: support.infomaniak.com
7. Use different passwords for each of your services
With a password manager such as BitWarden, you can easily create and securely save long and secure passwords for each of your online accounts.
8. Secure your accounts with two-factor authentication
By protecting your accounts with two-step verification, malicious people who have been able to obtain your password without your knowledge in a data leak will not be able to access them. Here’s how to activate this security at Infomaniak.
9. Check if your email address/password has been compromised
When a known site or service suffers a breach, sensitive information (such as passwords and email addresses) can be stolen by hackers. This information is then often resold or shared on the “dark web”. Hackers then use this information to try to access your accounts on other sites that you might use or send you phishing campaigns to obtain more sensitive information from you, such as banking information.
💡 You can check if your address and password have been affected by a known breach at haveibeenpwned.com
What does phishing look like? Real examples
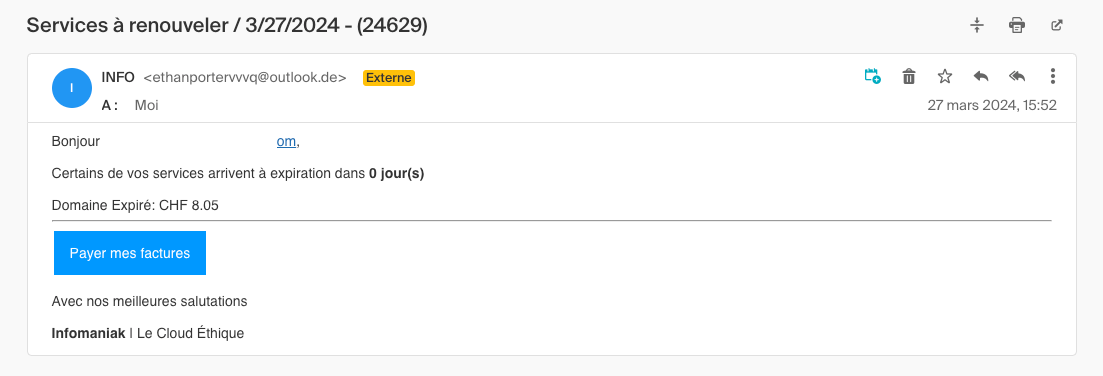
Here is an initial example of phishing that impersonates Infomaniak on the pretext of an invoice:
This scam can be thwarted in three ways:
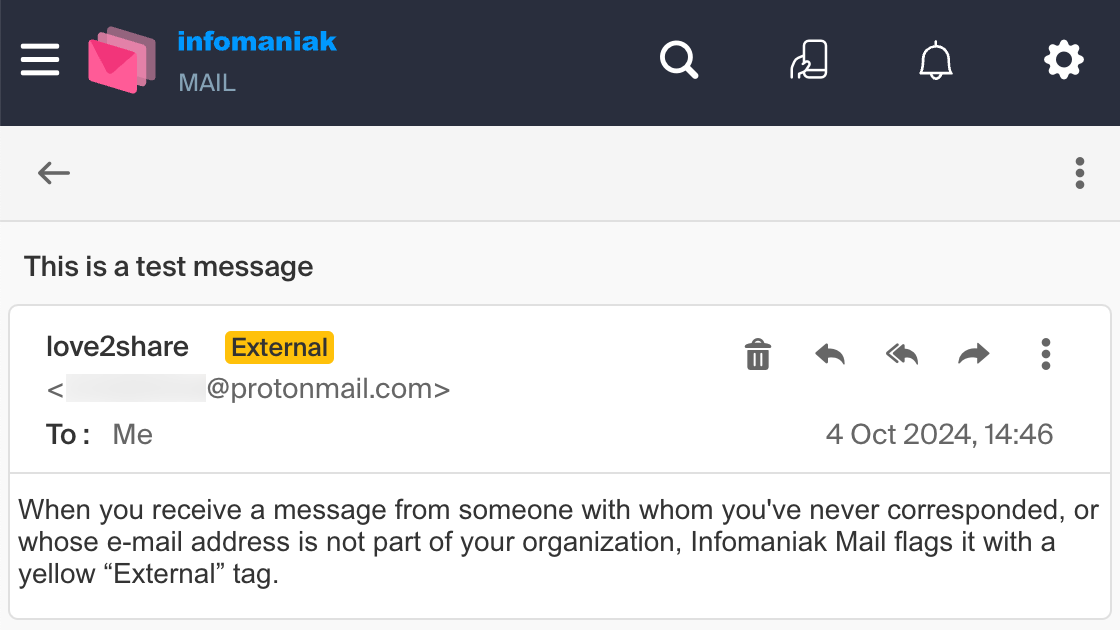
- With Infomaniak’s messaging service, an external yellow tag indicates that the email address is unknown to your contact database. When this tag appears, be vigilant and carefully check the email address you are writing to.
- The sender’s email address does not contain the @infomaniak.com domain
- The sender’s email address is not authenticated by a blue badge with a visa (see below).
Here’s a second example of phishing that impersonates Netflix:
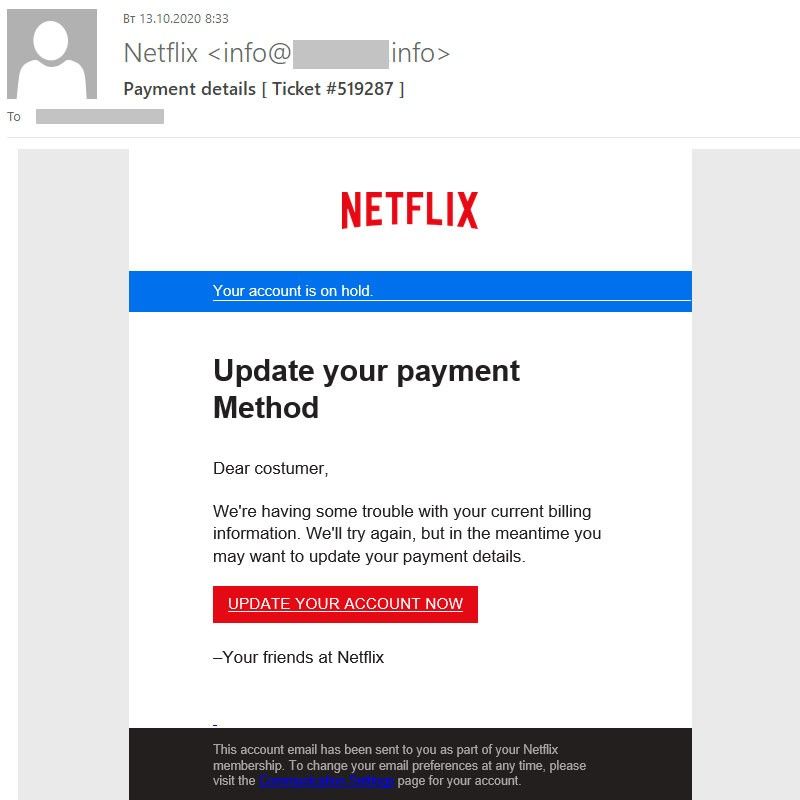
Again, the scam is detected by looking at the sender’s email address.
And here’s a third example of phishing that mimics a formal court summons:
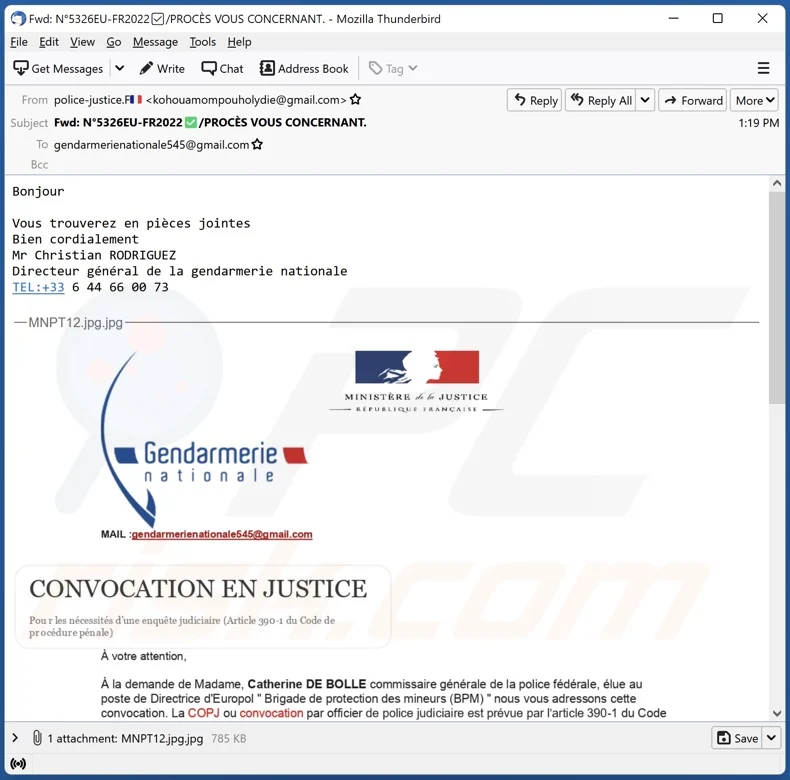
Again, the scam is thwarted by looking at the sender of the email.
What should you do if you have been fooled by a phishing attack?
- If you have already replied to a fraudulent email or receive persistent reminders, stop the correspondence immediately and delete the emails.
- If you’ve paid a ransom, you may have to file a complaint with the police and contact your bank to cancel your card and block the payment. In this case, keep all transaction messages and receipts.
- Scan your computer with a recognised anti-virus.
- Quickly change passwords for your social networks and any sensitive services you use. Here is the guide to modify your Infomaniak passwords.
- Report unsafe messages by following this guide.
⚠️ Infomaniak never asks you to provide your login credentials or any other personal information in an email (date of birth, address, bank details, etc.). Furthermore, our customers are continuously informed of any threats in the status of the services and in the Manager.
What is Infomaniak doing to combat phishing?
Infomaniak works continuously to protect its users as far as possible against cybersecurity threats by taking action on several fronts:
- Proactive blocking of unsafe sites and links.
- Security measures built into our messaging service, including free addresses.
- Continuous updating of our anti-spam filters to block threats upstream.
- Protection of our email infrastructure against identity theft and common threats.
- Prevention of our users via our status.infomaniak.com page and our social networks during mass campaigns aimed at Infomaniak.
- Submission of complaints to the police.
- Etc.
Useful resources
From UIKit to SwiftUI: developing an iOS mobile app with the latest Apple framework
Monday March 25th, 2024

 Français
Français Deutsch
Deutsch Italiano
Italiano Español
Español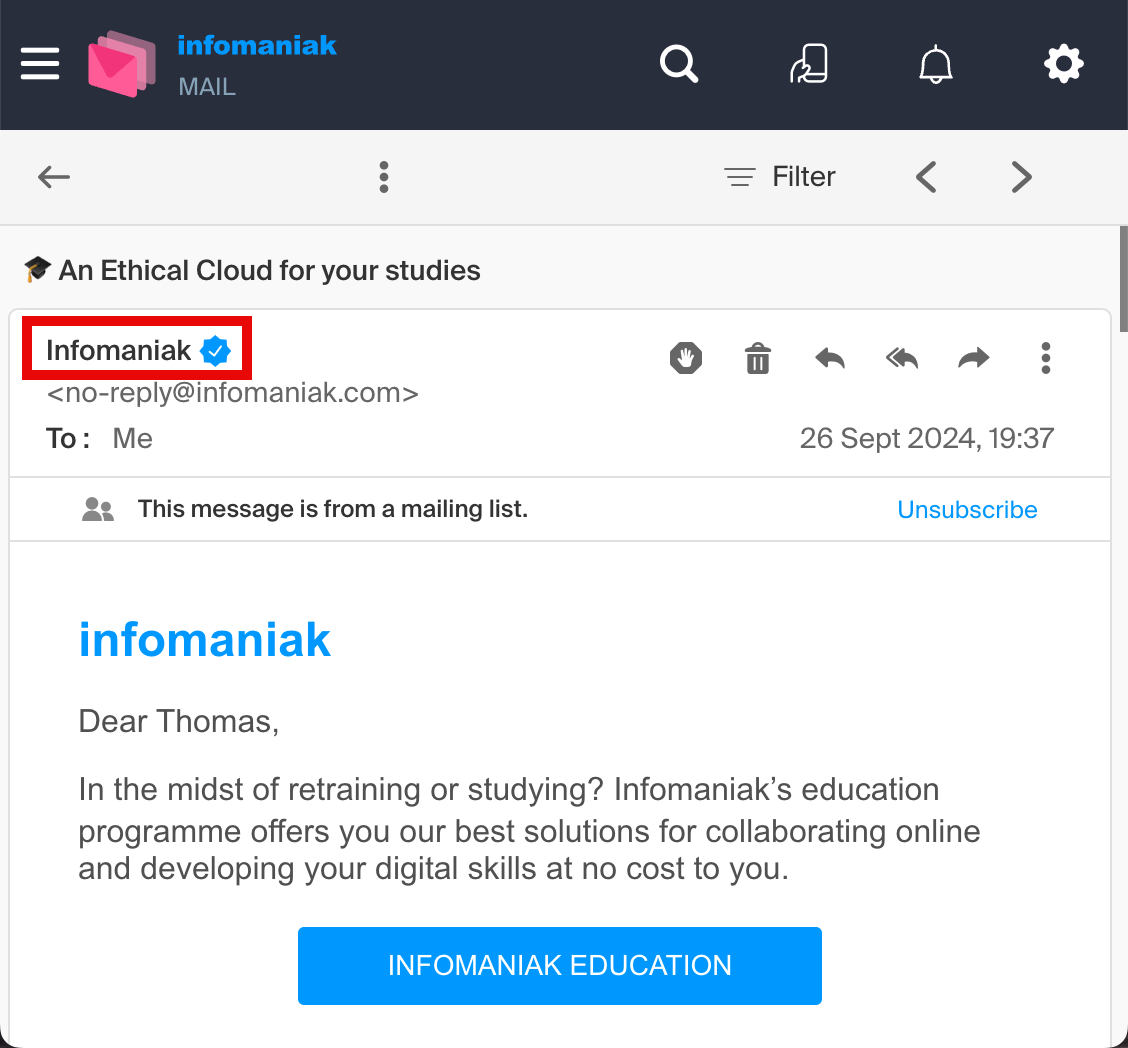





You must be logged in to post a comment.